Pegasus is a Spyware that was developed by NSO Group, an Israeli Cyber arms company. It can be secretly installed on most Android and iOS versions. According to Project Pegasus 2021, current Pegasus software can exploit all iOS versions until iOS 14.6. According to the Washington Post, Pegasus allows keystroke monitoring for all communications (texts and emails) but also allows phone call and location tracking. It also permits NSO Group to hijack the microphone and camera of a mobile phone, turning it into an ongoing surveillance device.
Military-grade spyware licensed by an Israeli firm to governments for tracking terrorists and criminals was used in attempted and successful hacks of 37 smartphones belonging to journalists, human rights activists, business executives and two women close to murdered Saudi journalist Jamal Khashoggi, according to an investigation by The Washington Post and 16 media partners.
According to The Washington Post, NSO Group said that its software can’t be used on US-issued phones. The investigation also found no evidence that Pegasus had successfully compromised US phones.
What is Pegasus?
Spyware is malicious software that can enter your device and gather your personal data without your consent.
NSO Group’s Pegasus is the most powerful spyware to date. It can infiltrate Android and iOS smartphones and make them surveillance devices.
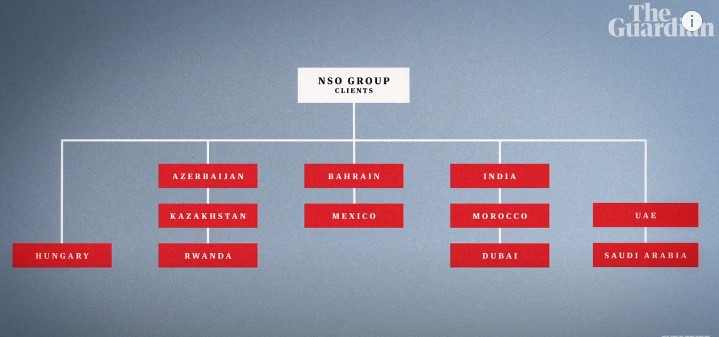
However, the Israeli company markets it as a tool for tracking criminals and terrorists, and not for mass surveillance. The software is sold by NSO Group to governments only. One license, which can be used on multiple smartphones, can cost up to Rs 70 lakh. NSO Group infected 10 smartphones with a $650,000 price list. The installation fee was $500,000.
How Does Pegasus Work?
Pegasus exploits unknown vulnerabilities in Android and iOS. Even if a security patch has been installed, a phone can still be infected.
An earlier version of the spyware, which was first introduced in 2016, infected smartphones by a technique known as “spear-fishing”. This involves sending malicious links to the target via text messages or email. It was dependent on the target clicking on the link, a requirement that was removed in later versions.
Pegasus could hack into a device using a missed WhatsApp call and delete the record, making it difficult for users to identify that they were targeted. WhatsApp revealed in May 2017 that Pegasus had exploited an error in its code to infect over 1,400 Android phones and iPhones. This included those belonging to journalists, government officials, and human rights activists. The bug was quickly fixed.
Pegasus exploits bugs in iMessage too, giving it access to millions of iPhones. It can also be installed on a wireless transceiver (radio transmitter/receiver) near a target.
Brief History of Pegasus – Captured From The Economic Times

2016: Canadian cybersecurity organization, The Citizen Lab was the first to encounter Pegasus via a smartphone belonging to Ahmed Mansoor, a human rights activist.
In September 2018: A report by the Citizen Lab identified 45 countries where Pegasus was used. The list also included India, as per the latest revelations.
Back in October 2019: WhatsApp revealed that Pegasus operators had used Pegasus to monitor journalists and activists in India.
Recent Revelation on July 2021: Pegasus Project is an international investigative journalism project that revealed how various governments used the software for spying on journalists, politicians, journalists and activists. The Pegasus Project revealed that the Indian government had used it to spy upon around 300 people between 2017-2019.
Pegasus Spyware Details
The spyware can be installed on certain versions of iOS, and some Android devices. Pegasus is not a single exploit. It’s a collection of exploits that exploits many weaknesses in the system. Clicking links, Google’s Photos app and the Apple Music app are all possible infection vectors. Pegasus exploits are zero-click, meaning they run without the victim’s interaction. Pegasus can be installed and run arbitrary code. It can extract contact information, call logs, message history, settings, and even gather information from communication apps like Viber, Gmail, Facebook, WhatsApp, Telegram and Skype.
Pegasus will hide as much as possible, and then self-destruct to remove evidence if it is unable to communicate for more than 60 days or on the wrong device. Pegasus can also perform this task at will.
How to Check Your Phone for Pegasus Spyware?
Amnesty International researchers have created a toolkit to help users determine if their phone has been infected with spyware.
Mobile Verification Toolkit is compatible with both iOS and Android OS. It makes it easier to acquire and analyse data from Android devices. Additionally, it analyzes files from iOS backups and filesystem dumps in order to detect potential compromise traces.
Alongside the tool is a great set of instructions, which should help you through the somewhat technical checking process. The tool allows you to back up your phone and run a check of that backup. If you have been squinting at your phone since the news broke, and want to learn more about Amnesty’s tool, read on.
But note that, the tool is terminal-based and command line-based. This means that it requires some technical skills or patience to use. Although we try to cover all the basics, it is important to be aware of some things before you jump in.
For detailed code check out https://www.amnesty.org/en/latest/research/2021/07/forensic-methodology-report-how-to-catch-nso-groups-pegasus/
Pegasus Spyware Removal
Pegasus spyware removal may not be the most pressing concern for you right now, especially since many anti-spyware programs and spyware removal tools will automatically detect and remove it for you. However, if you have sensitive data or financial information stored on your phone, you definitely do not want to take any chances with it getting stolen. No one wants to spend their life savings on an iPhone or other iOS device only to have that information stolen. With this in mind, you should make sure you are familiar with the different kinds of security measures you can use to protect yourself from potential spyware infections such as Pegasus.
Apple’s Action Against Pegasus Spyware
When news of the leak hit the news, Apple quickly launched an internal bug-bounty program for their devices. The company also patched all the various exploits the hackers had used against the iOS and Mac operating systems and issued a statement saying that they would not tolerate software that could be maliciously exploited to allow access to secure parts of the network. After a while, it seems that the Pegasus spyware did make it into the wild and had begun to pose a risk to the general iOS and Mac user community.
Coding Behind Pegasus
The computer code behind the Pegasus spyware is written in Objective C, which is the language commonly used by Apple developers. However, this code was hidden away within the code of a badly needed and unpopular commercial application called iOS Software. When the hackers released this software to the public, they inadvertently created a gateway to infiltrate many of the most widely used iPhones and iPad devices around the world. As a result, every person who has either purchased an iPhone, an iPad or an iPod Touch is vulnerable to being targeted by Pegasus.
The group calling themselves “hacktivists” behind the attack on iOS Software have created a video that they claim will show how easy it is to penetrate the iPhone spyware. It is important to note that despite the video being uploaded to YouTube, it has been confirmed that the hacktivist group has not released any compromising information regarding the inner workings of the iOS Software. It is also clear that the hacktivist group has not compromised any data on the actual iOS devices they have infected. The real question is why are these so-called “security researchers” looking to attack the most secure computer program on earth? Is it because they are tired of seeing the iPhone succeed and are feeling frustrated with the fact that its market has been dominated by Google’s Android operating system?
Whatever the reason, the Pegasus spyware infection should serve as a lesson to all of us that no matter how secure we think our iPhones and iPads are, we cannot expect to keep them entirely free of threat. While it is possible for the device’s manufacturer to release a patch to fix the problem, it is also a risk to consumers that buying an expensive phone from a major mobile network carrier could put our personal information at risk. By taking precautions to protect our mobile devices, we can limit the exposure of personal information to these attacks.
What is a Zero Day Attack?
Zero-days are computer-software vulnerabilities that are not known to anyone. Hackers can use the vulnerability to harm programs, data or networks until it is fixed.
A Zero day attack is when a hacker exploits a vulnerability before software developers are able to fix it.
Zero day vulnerabilities can be of any kind, as they can also manifest as a wider software vulnerability. They could be missing data encryption, SQL injection or buffer overflows. Missing authorizations can also occur. URL redirects, bugs and other security issues may also be present.
Zero day vulnerabilities are difficult to find proactively. This is in part good news as hackers will not be able to find them. It also makes it difficult to effectively guard against these vulnerabilities.
“When an iPhone is compromised, it’s done in such a way that allows the attacker to obtain so-called root privileges, or administrative privileges, on the device,” Claudio Guarnieri, who runs Amnesty International’s Berlin-based Security Lab told The Guardian. “Pegasus can do more than what the owner of the device can do.”
Google named the Android version of Pegasus, Chrysaorand and released security updates.
Can any Antivirus Detect the Malware Injected by Pegasus?
Antivirus software cannot detect malware it doesn’t already know about. In the case of Bhima Koregaon activists, it appears that malware called NetWire was infected in the computers of the defendants. McAfee antivirus detected it.
Pegasus could have created a new type of malware that McAfee and other anti-virus firms may not be aware of. It would be difficult to identify the malware. It is likely that many forensic labs are working hard to find the Pegasus malware.
Pegasus is not stopping them from creating new malware. They constantly check to see if any antivirus software was able to detect their malware. Pegasus will update its malware if and when this happens. This is an ongoing war.